
PhantomCall
Privacy-First, Web3-Native Video Calling
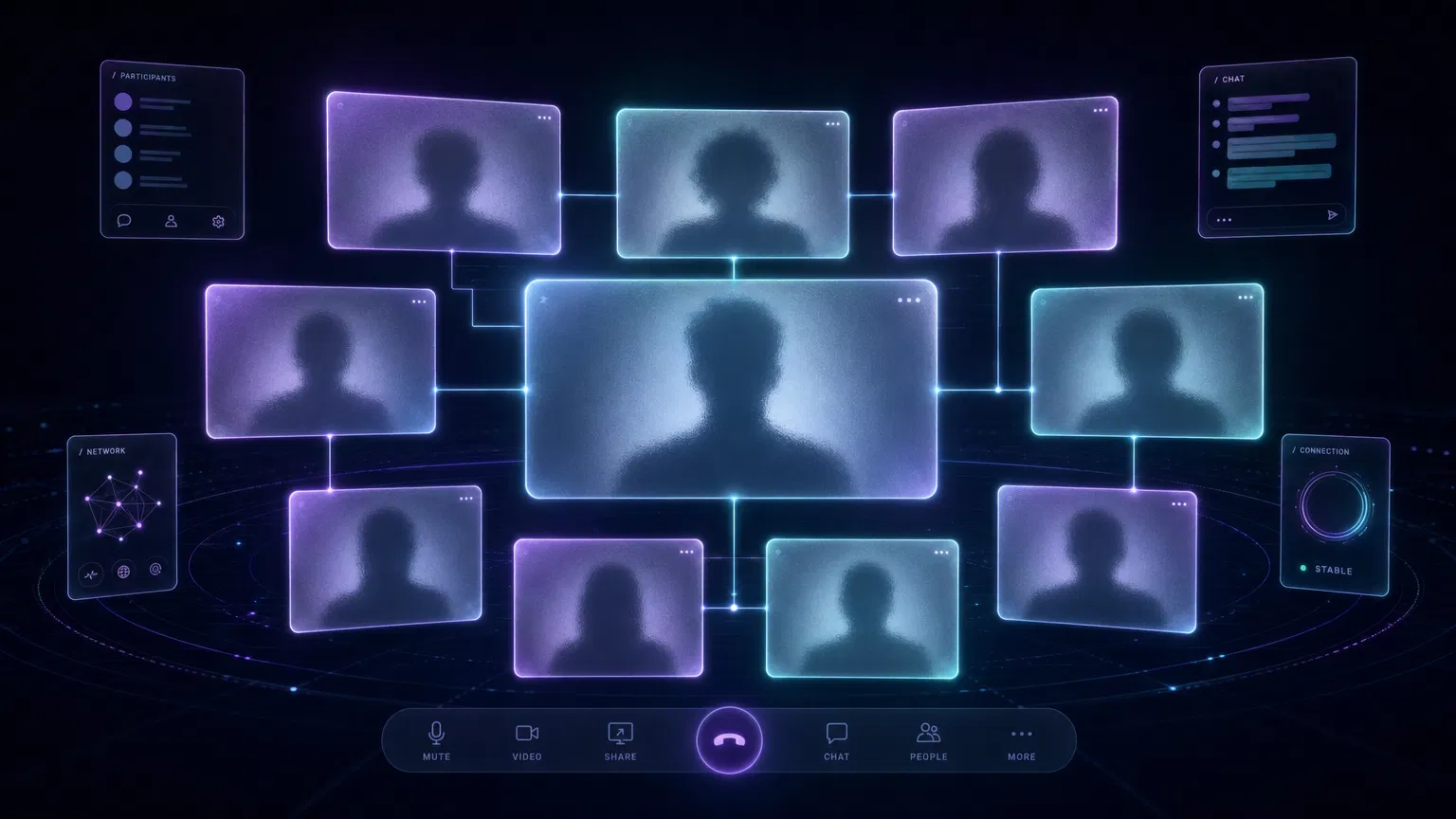
A globally distributed video calling platform with Solana wallet authentication, real-time human-blackout camera technology, and end-to-end encryption. Designed to outperform X (Twitter) for calls at every level.
Product Overview
A privacy-first, Web3-native video calling platform designed for secure, anonymous communication on a global scale.
Unlike traditional platforms such as Google Meet, Microsoft Teams, or X (formerly Twitter), this application integrates Solana wallet authentication via Phantom to ensure decentralized identity management without requiring personal information.
The core differentiator is a hardware-agnostic "human blackout" camera feature that utilizes real-time machine learning to completely remove the user's body from the video feed, displaying only their background. This ensures absolute visual privacy while maintaining the spatial context of a video call.
Built on a globally distributed WebRTC architecture, the platform delivers low-latency, high-quality audio and video communication internationally, specifically designed to outperform X's calling features by offering end-to-end encryption for all call types, superior video quality, dedicated meeting rooms, and robust cross-platform support.
User Roles
A streamlined user hierarchy focused on decentralized access.
Anonymous User
UnauthenticatedCan join existing calls via an invite link but cannot initiate calls, share screens, or access premium features. Subject to the same human-blackout privacy constraints as authenticated users.
Permissions
Authenticated User
Wallet ConnectedUsers who have connected their Phantom wallet and signed the authentication message. They can create private meeting rooms, generate invite links, initiate screen sharing, and manage privacy settings.
Permissions
Room Host
CreatorThe authenticated user who generated the meeting link. Possesses administrative controls including the ability to mute participants, remove users from the room, and lock the room to prevent new entries.
Permissions
Core Features
A focused set of features prioritizing privacy and performance.
Solana Wallet Authentication
Seamless login using Phantom Wallet, eliminating the need for email addresses, phone numbers, or traditional passwords.
Human-Blackout Video Feed
Real-time, client-side machine learning segmentation that completely obscures the human form while preserving the background environment.
Private Meeting Rooms
Ephemeral, secure video call rooms generated with unique cryptographic URLs. No accounts or social profiles required to join.
High-Fidelity Screen Sharing
Share entire screens, specific application windows, or individual browser tabs with optimized frame rates for text readability.
Global Low-Latency Routing
Distributed SFU architecture ensuring high-quality connections regardless of geographic location, surpassing the P2P limitations of X.
End-to-End Encryption
All media streams (audio, video, screen share) encrypted end-to-end using WebRTC's built-in DTLS/SRTP protocols.
Video Privacy Requirements
The human-blackout feature is the cornerstone of the platform's privacy guarantee.
Absolute Obfuscation
The human body, face, hands, and clothing must be fully blacked out or rendered entirely transparent. The system must err on the side of over-segmentation (blacking out parts of the background) rather than under-segmentation (revealing parts of the user).
Client-Side Processing
All video processing must occur locally on the user's device within the browser. Unprocessed video frames containing the user's image must never be transmitted over the network or sent to any server.
Real-Time Performance
The segmentation model must operate at a minimum of 24 fps on standard consumer hardware to ensure a smooth viewing experience without introducing significant latency.
Fail-Safe Mechanism
If the segmentation model fails to load, crashes, or cannot maintain the required frame rate, the camera feed must default to a completely black screen or a static placeholder image. The raw camera feed must never be exposed as a fallback.
Human-Blackout Pipeline
Raw video track obtained via getUserMedia
MediaStreamTrackProcessor extracts individual VideoFrame objects
Each frame passed to Web Worker running MediaPipe Selfie Segmentation
OffscreenCanvas isolates background pixels; human area filled with solid black (#000000)
Processed frames fed into MediaStreamTrackGenerator creating a privacy-safe video track
Implementation: Uses the Insertable Streams for MediaStreamTrack API. The MediaStreamTrackProcessor extracts frames, a TransformStream processes each through MediaPipe in a Web Worker, and the MediaStreamTrackGenerator outputs the privacy-safe stream.

Wallet Authentication Flow
Leverages the Sign-In With Solana (SIWS) standard for secure, passwordless access.
Connection Request
User clicks the "Connect Wallet" button on the landing page.
Wallet Prompt
The application invokes the Solana Wallet Adapter, prompting Phantom to request connection approval.
Challenge Generation
Upon approval, the backend generates a unique cryptographic challenge (nonce) and a timestamp.
Signature Request
The application requests the user to sign the challenge message using their Phantom Wallet, proving ownership of the associated public key without executing a blockchain transaction.
Verification & Session
The backend verifies the cryptographic signature against the user's public key. If valid, the server issues a secure JSON Web Token (JWT) to establish the session.

Key Libraries
Private Call Flow
Designed for security and ease of use.
Room Creation
An authenticated user clicks "Create Call." The backend generates a unique, cryptographically secure room identifier (UUIDv4) and provisions resources on the nearest SFU node.
Link Generation
The application provides the host with a unique invite link containing the room identifier.
Pre-Call Lobby
When any user navigates to the link, they enter a pre-call lobby. Camera and microphone permissions are requested. Human-blackout processing is initialized and previewed locally before joining.
Connection Establishment
Upon clicking "Join," the client establishes a secure WebRTC connection with the regional SFU, negotiating media capabilities and exchanging ICE candidates.
Media Routing
The SFU begins routing the encrypted audio and processed video streams between all participants in the room.
Technical Architecture
A globally distributed SFU architecture for low-latency, high-quality communication.
Client Application
A Single Page Application (SPA) built with React and TypeScript. Handles the user interface, wallet integration, and local media processing.
Signaling Server
A globally distributed WebSocket service responsible for room management, user presence, and WebRTC signaling (SDP offer/answer exchange).
Media Routing (SFU)
A cluster of SFU servers (LiveKit or Mediasoup) deployed in multiple data centers worldwide. Receives media from each participant and selectively forwards to others.
TURN/STUN Infrastructure
A global network of TURN/STUN servers to facilitate NAT traversal and ensure reliable connectivity for users behind restrictive firewalls.
Hover over a node to see details about each component.
Recommended Tech Stack
| Component | Technology |
|---|---|
| Frontend Framework | React + TypeScript |
| Wallet Integration | Solana Wallet Adapter |
| Video Processing | MediaPipe (Selfie Segmentation) |
| Stream Manipulation | Insertable Streams API |
| WebRTC Infrastructure | LiveKit (Open Source SFU) |
| Backend / Signaling | Node.js + WebSocket |
| Native Wrapper | Capacitor (Ionic) |
| Payments | Stripe Checkout + Webhooks |
| Push Notifications | APNs + FCM via Capacitor |
Security & Privacy
Every architectural decision prioritizes user privacy and data protection.
Zero-Knowledge Video
The server never receives unprocessed video frames. All human-blackout processing is strictly client-side. Raw camera data never leaves the user's browser.
IP Address Protection
Unlike P2P architectures (such as X's default calling mode), the SFU architecture masks user IP addresses. Participants only connect to the SFU, never directly to each other.
Ephemeral Data
Meeting rooms and associated signaling data are destroyed immediately upon the conclusion of the call. No media is recorded or stored on the servers.
Wallet Anonymity
The platform does not associate wallet addresses with real-world identities. The wallet address serves solely as a cryptographic identifier for session management.
Security Hardening
Defense-in-depth measures across headers, application logic, infrastructure, and media transport.
Content Security Policy (CSP)
HeadersStrict CSP headers enforced via meta tags and server response headers. Restricts script-src to 'self' and trusted CDNs (LiveKit SDK, MediaPipe WASM). Blocks inline scripts except those with nonces. Disallows eval() and data: URIs for scripts. frame-ancestors set to 'none' to prevent clickjacking.
default-src 'self'; script-src 'self' 'nonce-{random}' https://cdn.livekit.io https://cdn.jsdelivr.net; style-src 'self' 'unsafe-inline' https://fonts.googleapis.com; connect-src 'self' wss://*.livekit.cloud https://rpc.solana.com; media-src 'self' blob:; frame-ancestors 'none';
Input Sanitization & Validation
ApplicationAll user-controlled inputs (room names, display names, chat messages) are validated using Zod schemas on both client and server. HTML entities are escaped before rendering. Room IDs are UUIDv4 format-validated. Wallet addresses are validated against Solana's base58 format with checksum verification.
Zod schemas with .regex() for wallet addresses, .uuid() for room IDs, .max(50).trim() for display names. DOMPurify for any rich-text rendering.
Rate Limiting & DDoS Protection
InfrastructureMulti-layer rate limiting: Cloudflare WAF at the edge (50 req/s per IP), Express rate-limiter middleware on signaling server (10 room-create/min per wallet), and WebSocket connection throttling (max 5 concurrent per IP). Signaling messages rate-limited to 30/second per connection.
express-rate-limit with Redis store for distributed state. Cloudflare Workers for edge-level filtering. WebSocket heartbeat timeout at 30 seconds.
WebRTC Security Hardening
MediaDTLS 1.2+ mandatory for all peer connections. SRTP with AES-128-CM cipher for media encryption. ICE candidate filtering to prevent local IP address leakage via mDNS. TURN server authentication via time-limited HMAC credentials rotated every 6 hours.
RTCPeerConnection configured with iceTransportPolicy: 'relay' option available for maximum privacy. TURN credentials generated server-side with HMAC-SHA1 and 6-hour TTL.
Subresource Integrity (SRI)
HeadersAll externally loaded scripts and stylesheets include integrity attributes with SHA-384 hashes. This prevents CDN compromise or MITM attacks from injecting malicious code into the application.
Build pipeline generates SRI hashes for all external resources. CI/CD step validates hashes match expected values before deployment.
Secure Session Management
ApplicationJWT tokens issued with 1-hour expiry, stored in HttpOnly cookies (not localStorage) to prevent XSS token theft. Refresh tokens rotate on each use. Session invalidation on wallet disconnect. CSRF protection via SameSite=Strict cookie attribute.
jose library for JWT signing with Ed25519 keys. Cookie attributes: HttpOnly, Secure, SameSite=Strict, Path=/. Token refresh endpoint with rotation and reuse detection.
Cross-Platform Compatibility
Designed to work across every major platform, browser, and device class.
Browser & Platform Matrix
| Platform | Status |
|---|---|
| Desktop — Chrome/Edge | Full Support |
| Desktop — Firefox | Full Support |
| Desktop — Safari (macOS) | Partial Support |
| iOS — Safari / PWA | Supported |
| iOS — Capacitor Native | Full Support |
| Android — Chrome / PWA | Full Support |
| Android — Capacitor Native | Full Support |
Hardware Requirements
Segmentation runs at 15fps. Audio-only fallback if GPU unavailable.
Segmentation at 24fps. Smooth screen sharing at 1080p.
Segmentation at 30fps via WebGPU. 4K screen sharing. Multi-participant grid.
Niche & Edge Devices
Chromebooks
Full via Chrome browserARM-based Chromebooks may need reduced segmentation resolution (360p input). x86 Chromebooks perform comparably to desktop Chrome.
Linux Desktop
Full via Chrome/ChromiumPipeWire and PulseAudio both supported for audio. Screen sharing requires XDG Desktop Portal on Wayland.
iPad / Android Tablets
Full via browser or Capacitor appLandscape mode optimized for multi-participant grid. Split-screen multitasking supported on iPadOS 16+ and Android 12+.
Smart Displays (Nest Hub, Echo Show)
Not supportedThese devices use restricted browser engines without getUserMedia or WebRTC support. Not a target platform.
VR Headsets (Quest, Vision Pro)
ExperimentalMeta Quest Browser supports WebRTC. Apple Vision Pro's Safari supports WebRTC. Segmentation untested on these GPUs. Potential future expansion.
Raspberry Pi 4/5
LimitedChromium on Pi 4 can handle WebRTC audio/video. Segmentation too slow for real-time (sub-10fps). Audio-only mode recommended.
Subscription Plans
Transparent, wallet-native pricing powered by Stripe. No personal information required.
Free
Pro
PopularEnterprise
Stripe Integration Flow
Wallet-to-Customer Mapping
When a user first upgrades, the backend creates a Stripe Customer object linked to their Solana wallet public key (stored as customer metadata). No email or personal information is required. The mapping is stored in the database as wallet_address → stripe_customer_id.
Checkout Session Creation
The backend creates a Stripe Checkout Session with the appropriate price ID, the customer ID, and success/cancel URLs. The session is configured for 'subscription' mode with automatic tax collection disabled (crypto-native users).
Payment Processing
The user is redirected to Stripe's hosted checkout page. Stripe handles PCI-compliant card collection, 3D Secure authentication, and payment processing. No card data ever touches PhantomCall servers.
Webhook Verification
Stripe sends webhook events (checkout.session.completed, invoice.paid, customer.subscription.updated, customer.subscription.deleted) to the backend. Each event is verified using the webhook signing secret before processing.
Entitlement Enforcement
The backend updates the user's subscription tier in the database. The SFU and signaling server check entitlements before allowing tier-gated features (group calls, HD streaming, recording). JWT tokens include the subscription tier claim.
Payment Security Measures
App Store & Play Store Deployment
Native distribution via Capacitor (by Ionic) — reusing 100% of the React codebase.
Capacitor (by Ionic)
Capacitor wraps the existing web application in a native shell, providing access to native APIs (push notifications, background audio, biometrics) while reusing 100% of the React codebase. Unlike Cordova, Capacitor uses modern WKWebView on iOS and Chrome Custom Tabs on Android.
iOS App Store Deployment
Apple Developer Account
Enroll in the Apple Developer Program ($99/year). Required for App Store distribution, push notification certificates, and TestFlight beta testing.
Provisioning & Certificates
Create an App ID with Push Notifications and Associated Domains capabilities. Generate a distribution certificate and provisioning profile in the Apple Developer portal.
Build & Archive
Run npx cap sync ios to copy web assets. Open the Xcode project (npx cap open ios). Set the bundle identifier, version, and build number. Archive the build via Product → Archive.
App Store Connect Submission
Upload the archive to App Store Connect via Xcode Organizer. Fill in app metadata: description, screenshots (6.7" and 5.5" required), privacy policy URL, and age rating (4+ with no objectionable content).
App Review
Submit for review. Typical review time is 24-48 hours. Key review considerations: explain camera usage for privacy (not surveillance), demonstrate the human-blackout feature in screenshots, and provide a demo account or invite link for the reviewer.
Privacy Nutrition Labels
Declare data collection practices: Camera (used for video calls, not linked to identity), Microphone (used for audio, not linked to identity), Identifiers (wallet address, not linked to real identity). Mark 'Data Not Collected' for all other categories.
Google Play Store Deployment
Google Play Developer Account
Register for a Google Play Developer account ($25 one-time fee). Complete identity verification and accept the Developer Distribution Agreement.
Signing Key Setup
Generate an upload key using keytool. Enroll in Google Play App Signing (recommended) to let Google manage the app signing key. Configure the upload key in capacitor.config.ts.
Build AAB
Run npx cap sync android to copy web assets. Open Android Studio (npx cap open android). Build a signed Android App Bundle (AAB) via Build → Generate Signed Bundle.
Play Console Submission
Create a new app in Google Play Console. Upload the AAB. Fill in store listing: title, short/full description, screenshots (phone and 7" tablet required), feature graphic (1024x500), and privacy policy URL.
Content Rating & Data Safety
Complete the content rating questionnaire (IARC). Fill in the Data Safety form: Camera and Microphone used for video calls (not shared with third parties), no personal data collected, wallet address used for authentication only.
Release Track
Start with Internal Testing (up to 100 testers) → Closed Testing (up to 1000) → Open Testing → Production. Each track requires review approval. Production review typically takes 1-3 days.
Deployment Risks & Mitigations
Apple WebRTC Restrictions
MediumWKWebView supports WebRTC since iOS 14.3. Capacitor's default WebView is WKWebView. Test on iOS 14.3+ as minimum deployment target.
Google Play Camera Policy
LowClearly explain camera usage in the Data Safety section. The human-blackout feature enhances privacy, which aligns with Google's user safety goals.
App Store Rejection — Crypto/Wallet
MediumPhantom Wallet is used solely for authentication, not for cryptocurrency transactions within the app. Frame the wallet as a 'decentralized login' method in the review notes. Do not mention trading, tokens, or DeFi.
Background Audio Termination
HighiOS aggressively kills background processes. Use Capacitor's background-runner plugin and configure AVAudioSession category to .playAndRecord with .mixWithOthers option. Test with screen off and app switcher.
WebView Performance on Low-End Devices
MediumImplement adaptive quality: detect device capabilities at startup (navigator.hardwareConcurrency, GPU renderer string). Downgrade segmentation to 15fps or 360p input on low-end devices. Provide audio-only fallback.
Push Notification Delivery
LowUse both APNs (iOS) and FCM (Android) via Capacitor push plugin. Implement in-app polling as fallback. Test notification delivery across different network conditions and battery saver modes.
Vultr Infrastructure Deployment
33 global regions. Vultr provides 33 global data center regions with NVMe-backed high-frequency compute, bare-metal options, and competitiv...
Recommended Instance Configuration
Signaling Server
High FrequencyHandles WebSocket connections, room management, wallet auth verification, and WebRTC negotiation. Stateless — horizontally scalable behind a load balancer.
NVMe critical for Redis co-location. 3 TB bandwidth included per instance.
LiveKit SFU Node
High FrequencySelective Forwarding Unit for media routing. CPU-intensive — each node handles ~50–100 concurrent participants depending on video resolution and simulcast layers.
Scale horizontally. Add nodes per region as user base grows. 4 TB bandwidth per instance.
TURN/STUN Server (coturn)
Cloud Compute (Regular)NAT traversal relay for users behind restrictive firewalls. Bandwidth-intensive — handles relayed media streams when direct P2P fails.
TURN traffic consumes bandwidth. Monitor overage at $0.01/GB. Consider upgrading to High Frequency if relay usage exceeds 30%.
PostgreSQL Database
Vultr Managed DatabaseStores wallet-to-customer mappings, subscription tiers, room metadata, and audit logs. Single-writer with read replicas.
Managed PostgreSQL includes automated backups and failover. SSL enforced.
Redis Cache
Vultr Managed DatabaseSession store, rate limiting counters, pub/sub for signaling coordination, and TURN credential caching.
Co-located with primary signaling server for lowest latency.
Monthly Cost Breakdown (MVP)
| Resource | Monthly Cost |
|---|---|
| Signaling Servers (2× HF $24) | $48 |
| LiveKit SFU Nodes (4× HF $48) | $192 |
| TURN/STUN Servers (4× Regular $20) | $80 |
| PostgreSQL Managed DB (primary + replica) | $30 |
| Redis Managed Cache | $15 |
| Snapshots & Backups (estimated) | $20 |
| Extra IPv4 Addresses (4×) | $12 |
| Bandwidth Overage Buffer (100 GB) | $1 |
| Total (MVP Baseline) | $398/month |
$398/month
Baseline for up to ~400 concurrent users across 4 regions
$800–$1,200/month
8–12 SFU nodes, dedicated TURN, higher bandwidth allocation for 2,000+ concurrent users
$2,500+/month
Bare metal SFU nodes, dedicated database clusters, 10+ regions, 10,000+ concurrent users
Recommended Regions
New Jersey, US
ewrLowest latency to US East Coast. Co-locates signaling, DB, and Redis.
Amsterdam, NL
amsCentral Europe coverage. GDPR-compliant data residency.
Singapore, SG
sgpCovers Southeast Asia, India, and Oceania.
Tokyo, JP
nrtJapan, Korea, and East China coverage.
São Paulo, BR
gruLatin America coverage. Reduces 200ms+ latency from US-East.
London, UK
lhrUK and Northern Europe. Add when EU traffic justifies a second node.
Mumbai, IN
bomIndia subcontinent. Add when APAC user base grows beyond Singapore capacity.
Sydney, AU
sydAustralia and New Zealand. Add for Oceania-specific latency requirements.
Deployment Pipeline
Provision Infrastructure via Vultr API
Use Terraform with the Vultr provider (vultr/vultr) to declaratively provision all instances across target regions. Store Terraform state in Vultr Object Storage or a remote backend. Tag all resources with environment (prod/staging) and role labels.
Configure Networking & Firewall
Create a Vultr VPC in each region for private networking between SFU and signaling nodes. Configure firewall groups: allow TCP 443 (HTTPS), UDP 3478 (TURN), UDP 10000-60000 (WebRTC media), and TCP 7880-7881 (LiveKit). Block all other inbound traffic.
Deploy with Docker Compose or Kubernetes
Package LiveKit, signaling server, and coturn as Docker images. For MVP, use Docker Compose on each node with Watchtower for automated updates. For scale, migrate to Vultr Kubernetes Engine (VKE) with Helm charts.
Configure DNS on Namecheap
Point your domain's A records to Vultr instance IPs. Use Cloudflare as a DNS proxy for DDoS protection and SSL termination. Set up subdomain routing: app.yourdomain.com → signaling, sfu-{region}.yourdomain.com → SFU nodes, turn-{region}.yourdomain.com → TURN servers.
SSL/TLS Certificates
Use Let's Encrypt with Certbot for automated certificate provisioning and renewal. Configure Nginx or Caddy as a reverse proxy with HTTP/2 and HSTS headers. For TURN servers, use the same wildcard certificate across all regions.
Monitoring & Alerting
Deploy Prometheus + Grafana on a dedicated $6/month High Frequency instance. Monitor SFU CPU usage, WebSocket connection counts, TURN relay bandwidth, and database connection pools. Set alerts for >80% CPU, >90% memory, and TURN bandwidth spikes.
CI/CD Pipeline
GitHub Actions workflow: build Docker images → push to Vultr Container Registry → SSH deploy to each region via Ansible or Terraform apply. Blue-green deployment strategy with health checks before traffic cutover.
Scaling Strategy
| Phase | Users | Cost |
|---|---|---|
| MVP Launch | 0–500 concurrent | ~$398/mo |
| Growth | 500–2,000 concurrent | ~$800/mo |
| Scale | 2,000–10,000 concurrent | ~$2,000/mo |
| Enterprise | 10,000+ concurrent | $3,000+/mo |
Namecheap DNS Configuration
Connect your Namecheap domains to Vultr infrastructure with Cloudflare as a security proxy.
Switch to Custom DNS or Cloudflare
In Namecheap dashboard, go to Domain List → Manage → Nameservers. For direct Vultr pointing, select 'Custom DNS' and add Cloudflare nameservers (e.g., ns1.cloudflare.com, ns2.cloudflare.com). This enables Cloudflare's proxy, DDoS protection, and SSL termination in front of Vultr.
Configure A Records
In Cloudflare (or Namecheap Advanced DNS), create A records: '@' → Vultr signaling server IP (proxied), 'app' → same IP (proxied), 'sfu-us' → US SFU node IP (DNS only — WebRTC needs direct IP), 'turn-us' → US TURN server IP (DNS only).
Configure SRV Records for TURN
Add SRV records for TURN discovery: _turn._udp.yourdomain.com → turn-{region}.yourdomain.com:3478. This enables automatic TURN server selection based on client region.
Enable DNSSEC
In Cloudflare, enable DNSSEC under the DNS tab. Copy the DS record values to Namecheap: Domain List → Manage → Advanced DNS → DNSSEC. This prevents DNS spoofing attacks that could redirect users to malicious servers.
Verify Propagation
Use dig or nslookup to verify all records resolve correctly. DNS propagation typically takes 1–48 hours. Test WebRTC connectivity from multiple regions using webrtc.github.io/samples to confirm TURN/STUN resolution.
Example DNS Record Layout
A @ → 149.28.x.x (Proxied)
A app → 149.28.x.x (Proxied)
A sfu-us → 45.76.x.x (DNS Only)
A sfu-eu → 95.179.x.x (DNS Only)
A sfu-sg → 139.180.x.x (DNS Only)
A sfu-jp → 64.176.x.x (DNS Only)
A turn-us → 45.32.x.x (DNS Only)
SRV _turn._udp → turn-us:3478 (Priority 10)
Note: SFU and TURN records must be DNS Only (not proxied) because WebRTC requires direct UDP connectivity. Only the signaling/app endpoints should be Cloudflare-proxied for DDoS protection.
Deployment Files
Production-ready infrastructure-as-code files. Export to GitHub and run on your Vultr VPS.
Terraform (Vultr)
main.tf
Multi-region Vultr instances, VPC, firewall rules
variables.tf
Configurable parameters (regions, plans, secrets)
outputs.tf
IP addresses, DNS records, cost estimates
terraform.tfvars.example
Template for your credentials
Docker Compose
docker-compose.yml
Full stack: LiveKit, coturn, signaling, PostgreSQL, Redis, Nginx
Dockerfile.signaling
Node.js signaling server image
Dockerfile.webapp
Static frontend Nginx image
livekit.yaml
LiveKit SFU server configuration
turnserver.conf
coturn TURN/STUN configuration
001-schema.sql
PostgreSQL database schema
Nginx
nginx.conf
Main config with rate limiting and security headers
phantomcall.conf
Site config: SSL, CSP, WebSocket proxy, CORS
CI/CD
deploy.yml
GitHub Actions: lint → test → build → deploy → smoke test
Mobile (Capacitor)
capacitor.config.ts
iOS + Android wrapper configuration
Info.plist.additions
iOS permissions, deep links, Phantom wallet
AndroidManifest.additions.xml
Android permissions, foreground service, deep links
How to Use These Files
- Export this project to GitHub via Management UI > Settings > GitHub
- Clone the repo on your local machine and navigate to the deployment/ directory
- Follow the deployment/README.md for step-by-step instructions
- Run terraform apply to provision Vultr infrastructure
- Run docker compose up -d on each server to deploy the stack
Competitive Advantage over X (Twitter)
Addressing the significant limitations present in X's current communication infrastructure.
| Feature | X (Twitter) | PhantomCall |
|---|---|---|
| Architecture | Primarily P2P (exposes IP by default) | Multi-Region SFU (masks IP, optimizes global routing) |
| Group Calls | Limited (No Android, no E2EE) | Fully supported across all platforms with E2EE |
| Screen Sharing | Web only | Supported on all compatible platforms |
| Authentication | Tied to public social media profile | Anonymous Web3 Wallet (Phantom) |
| Visual Privacy | None (standard camera feed) | Hardware-agnostic Human-Blackout |
| Access Model | Requires prior DM exchange | Instant access via secure invite links |
| International Infra | No optimization mentioned | Multi-region SFU with global TURN/STUN |
| IP Protection | Optional (off by default) | Always-on (SFU architecture) |
| Mobile Apps | Built into X app (limited features) | Dedicated PWA + native apps (Capacitor) |
| Subscription Model | X Premium required for some features | Free tier + transparent Pro/Enterprise pricing |
MVP Feature List
The Minimum Viable Product focuses on delivering the core value proposition.
Phantom Wallet connection and authentication
Creation of unique, shareable meeting links
Real-time human-blackout video processing (client-side)
Multi-participant audio and video routing via a single-region SFU
Basic screen sharing capabilities
Pre-call lobby for hardware testing and privacy verification
PWA installable on iOS and Android
Free tier with 1-on-1 calls and 30-minute limit